Encryption has been around for so long that you would gasp. The Roman legions used a substitution cypher (an early form of encryption) during the Gallic wars (and probably before that). Code books have long been used commercially where you could do word substitution. For instance, you would look up the word "ammunition" in a code book and put the letter group "GXQLY" in your message. Then the person with the OTHER half of the code book could look up GXQLY and write down ammunition. That was around AT LEAST during the Renaissance. Such books had ways for you to spell out a word or name not found in the code book.
During WWII, a unique verbal cypher method was devised using the Navajo "code talkers" - people who spoke the Navajo language and English. The trick here is simple: Navajo has no roots in common with any European or Oriental language and has no written alphabet. Therefore, when the Axis powers heard it spoken over the radio, it was total gibberish to them.
The advent of other types of cyphers is more recent because of the arduous nature of the substitution methods. However, the use of something as simple as an XOR (binary) sequence led to many of the modern cyphers. In Arabic, the word for zero is
sifr, so the origin of the name is easy enough.
Here is an article with some historical comments on cypher (or cipher) methods.

en.wikipedia.org
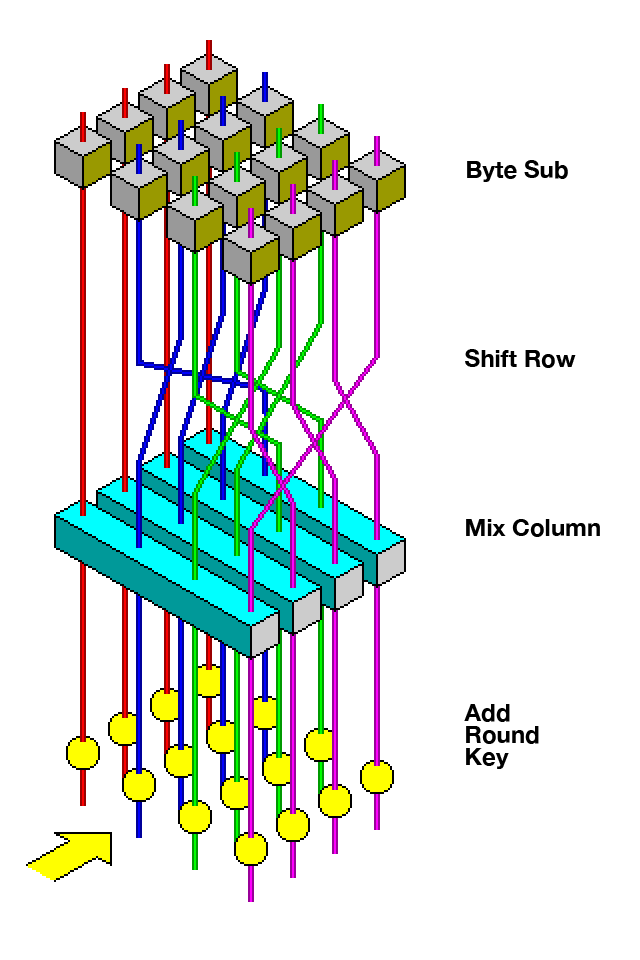
Modern encryption involves creation of a key that will be used to alter a given sequence of information, but true encryption must be Hermetian (the mathematical term for "reversible"). So typical methods will be to create long keys for which an XOR or other type of transform will be used. The trick will be to generate the key on the other end so you can perform the reverse operation. Key length is therefore part of the discussion for encryption methods. The "Advanced Encryption Standard" (AES) discusses keys of length 128, 192, or 256 bits. There are other standards besides AES.

en.wikipedia.org
There is such a thing as "hashing" that is NOT reversible, but that can be used to prove that a given message has not been altered. There, it doesn't matter if the formula is reversible, and in fact it usually is not. The idea is that if you get message X and separately get the hash for message X, you can compute the hash for yourself and compare that to the transmitted hash. If your hash matches the transmitted hash, the odds are very high that the message made it to you intact.
Encryption, Hashing, and Salting are three different concepts for three different purposes. Learn about what they do here.

www.thesslstore.com
That should be enough to get you thinking.